FireEye: Russian Research Lab Aided the Development of TRITON Industrial Malware Cybersecurity firm FireEye claims to […]
The future of OT security in modern industrial operations Both the likelihood and consequences of cyberattacks […]
DHS Warns of Threats to Precision Agriculture Relying on various embedded and connected technologies to improve […]
California’s new laws bolster security for connected devices California just raised the baseline for security in […]
Legitimate RATs Pose Serious Risk to Industrial Systems A report published on Friday by the security […]
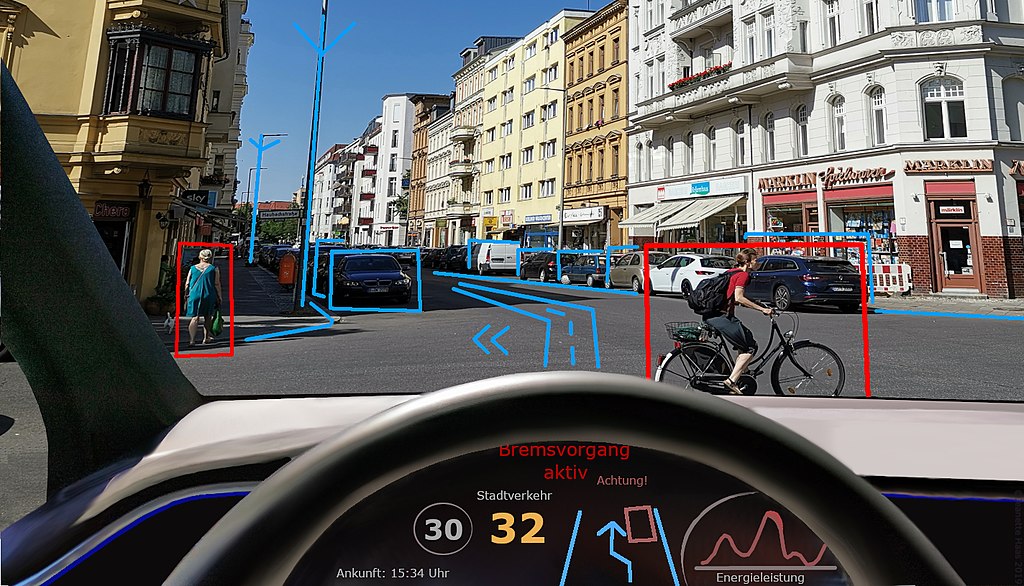
Be smart: Security is among the most difficult issues for AVs. Where the once distinct domains of automobiles and cybersecurity have collided, good-faith collaboration can make new forms of mobility safer, sooner.
Global market for smart city platforms expected to reach $755 million by 2027 Driven by Internet […]
Malware Found on USB Drives Shipped With Schneider Solar Products Schneider Electric recently informed customers that […]
Trend Micro’s new program helps IoT device makers tackle risk at source Trend Micro has reconfirmed […]
Hacking Police Bodycams Mitchell even realized that because he can remotely access device storage on models […]