We asked Hack The Sea about their work tackling security challenges in the maritime sector and the importance of protecting maritime systems from malicious actors.
Supply Chain Sandbox events at RSA featured interactive games that engaged participants in simulations to improve supply chain security skills, development, and teamwork.
I Am The Cavalry’s Josh Corman and Beau Woods were featured in The Verge for their work protecting the vaccine supply chain.
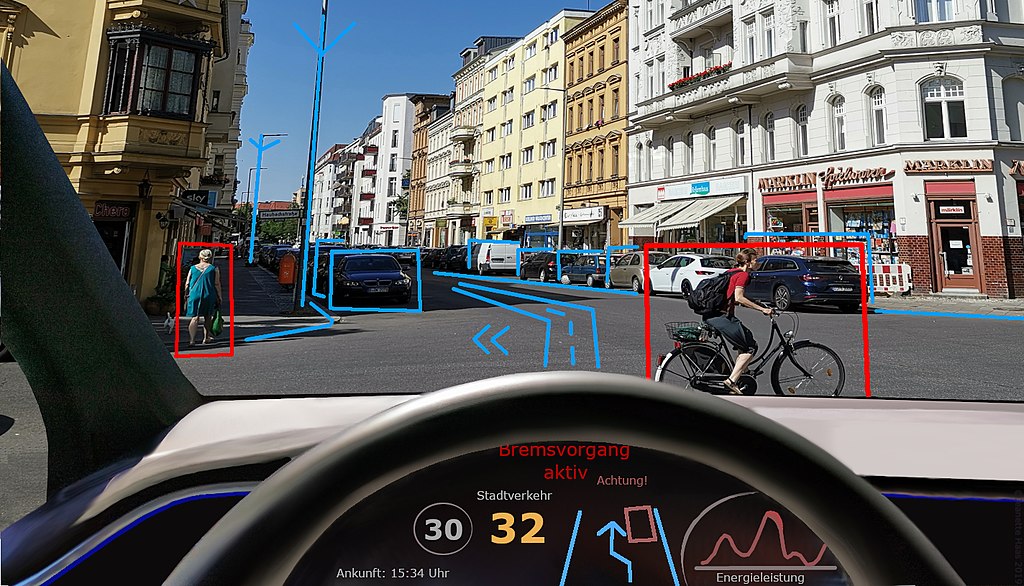
We asked the Car Hacking Village about their work providing hands-on security training and working together to inform the public and automotive industry.
We asked the IoT Village about how they help industry and threat researchers work together to secure our ever-growing number of connected devices.
I Am The Cavalry spoke with the Aerospace Village team about their work.
I Am The Cavalry’s Beau Woods joined The Internet of Things Podcast to discuss the hack of a water treatment plant in Florida and the general threat landscape of IoT.
I Am The Cavalry’s Josh Corman discussed the changes in the supply chain threat landscape as a result of vaccine distribution with The Washington Post.
I Am The Cavalry co-founder Josh Corman’s previous quotes on the threat of ransomware to the health sector were featured in a Decrypt "chainanalysis" on the rise in crypto ransomware payments.
I Am The Cavalry’s Beau Woods joined Threatpost for conversation on cybersecurity challenges for hospitals during the COVID-19 pandemic.